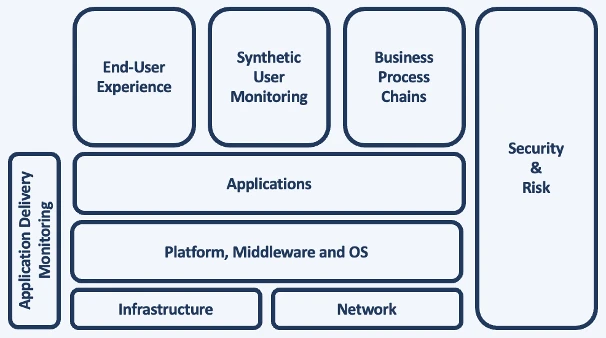
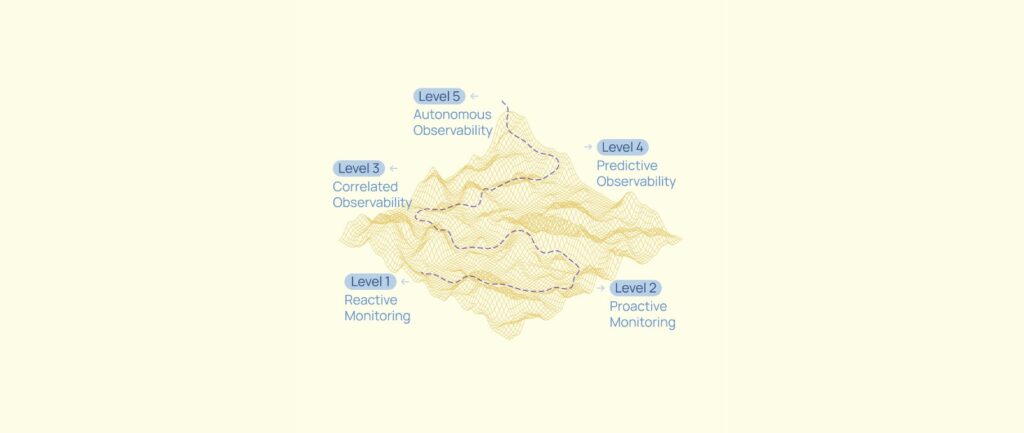
What we see with customers is a clear pattern. In early maturity, teams focus on the basics: infrastructure and application health. As maturity grows, the focus shifts outward to the layers where decisions and risk live. That is where security and risk management, end user experience, and business process chains come into focus.
That shift is where things get interesting. Because once you start observing outcomes instead of components, you inevitably hit overlapping capabilities with other (common) platforms, such as product analytics, BI and SIEM.
That is when the recurring questions show up:
“(Why) Should we invest in this capability, and where does it create value?”
“Who owns what across teams and platforms?”
“Can observability cover this, or is this a different discipline?”
In this blog, we give a practical overview of how these platforms differ, where the overlap is real, and how to make clean choices without duplicating efforts or creating governance friction.
Digital experience Analytics vs End-User experience observability
Also known as web- or product experience analytics, Digital Experience Analytics (DXA) is best known through platforms like Google Analytics. These type of platforms create behavioural abstractions of how end users move through digital journeys. They aim to answer a broad question: “What are users doing, and where does the journey seem to break down?
That is fundamentally different from end user experience observability capabilities within observability platforms, such as Real User Monitoring (RUM). The focus for these capabilities stay closer to the system and ask: “How is the system behaving as experienced by real users, right now and over time?” In practice, the two are distinct in goal, approach, and underlying technology.
Ownership of a DXA platform is not always straightforward and depends on the organisation’s structure. DXA has a distinct purpose, vocabulary and process, with overlap into both observability and BI. Therefore, it can sit with either domain or with a specialised team. Either way, the most important thing is that ownership is clearly established.
Business Intelligence vs Business Process Chains observability
At first glance, observability platforms can appear to overlap with BI, especially when they support capabilities like capturing business events and storing data in a lakehouse. However, just like DXA platforms, the purpose is fundamentally different. Some of the underlying mechanisms may still overlap, such as real-time ingestion and storage.
BI typically relies on precise, governed, and trusted ‘metrics’ to steer the company over the mid to long term. Business-focused capabilities within observability, on the other hand, connects system signals to business impact and turn incidents into clear, real-time actions.
BI platforms typically already have a specialised team and dedicated ownership. The main challenge is aligning with that team and making the distinction in goals explicit, so both platforms complement each other instead of competing for the same space.
Security Information & Event Management vs Security & Risk observability
From a distance, SIEM and observability platforms seem to do the same thing: both detect abnormal or suspicious behaviour based on system telemetry. However, when we look more closely, they serve different use cases. They also come with requirements that are hard to unify in a single platform, such as cardinality, legal constraints, retention, volume, and tamper resistance.
A SIEM is designed around security operations and case management aspect. It is the place where analysts investigate, correlate, escalate, and respond to potentially malicious activity. Observability platforms, by contrast, are built to improve reliability and performance. Teams use them to alert on anomalies, investigate root causes, and validate fixes for system failures.
There is some overlap, especially in the investigation workflow. That is where observability’s security & risk capabilities add value. They can enrich SOC investigations with additional context, and, in some cases, forward relevant events into the SIEM.
Ownership of SIEM platform is typically a clear responsibility of an IT security team or the SOC. The main challenge for observability teams is to understand what capabilities can support the SOC and to treat security as a first class stakeholder in the observability strategy.
Closing thoughts
As we have seen, there is a reason for each system’s existence. Some observability capabilities aim to fill gaps left by other platforms, which can look like overlap at first glance. However as vendors often over-market what their platforms can do, it is important to take a critical look at what you already have, what you truly need, and where each capability belongs.
If you face these questions and would like some advice, don’t hesitate to reach out!